Chinese hackers attack Russian officials

A few weeks ago, European politicians were still the focus of Chinese hacker attacks. Now the criminals are targeting Russian officials – presumably on behalf of the Chinese government.
At the beginning of the war in Ukraine, Chinese hackers targeted Ukrainian politicians in order to obtain information relevant to the war and to weaken the country’s infrastructure with targeted attacks.
Now, however, the attackers’ focus seems to have shifted: security researchers have discovered that Russian officials are said to be the latest victims of cybercriminals.
Hacker collective “Mustang Panda”
The responsible hacker collective is “Mustang Panda”, which, according to insider information, is indirectly active in intelligence on behalf of the Chinese government and collects sensitive data.
The hacker group has already attracted attention with numerous attacks on European government officials. It was only in March that “Mustang Panda” tried to use phishing messages to attack diplomatic missions and refugee facilities in Europe and to obtain non-public information.
Russia always in view of the attackers
As the experts report, Russia has never completely disappeared from the hackers’ sight, but the attacks have been scaled back as much as possible because China and Russia share similar geopolitical views.
However, as the cybersecurity firm Secureworks has now made public in its latest report, there is new evidence of Chinese attacks on Russian government officials, which amounts to a strategic paradigm shift by the Chinese government.
In their analysis, the experts assume that the changing war situation in Europe is the reason for the change of direction and that China’s focus may have shifted as a result.
Malware disguised as a harmless PDF document
The latest attacks are also phishing attempts, in which the hackers try to gain access to the systems of their Russian victims through infected fake documents.
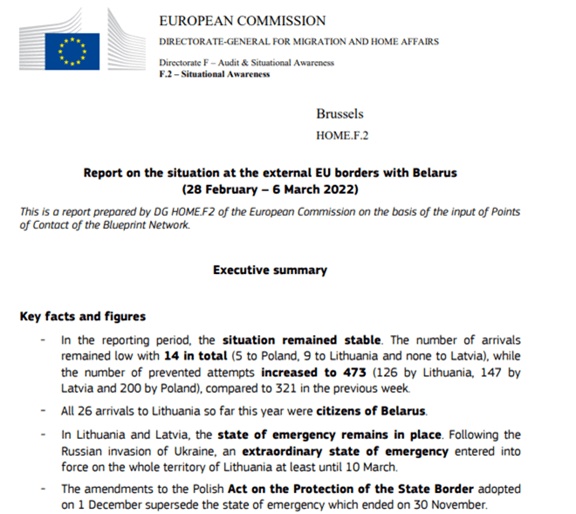
The defective .exe files are disguised as an alleged PDF document from the European Commission, in which sanctions against Belarus are listed and the refugee situation in the Baltic states bordering Belarus and in Poland is discussed.
In order to suggest the authenticity of the documents, they also bear the name of the Russian-Chinese border town “Blagoveshchensk” (German spelling: Blagoveshchensk). This leads the analysts to the conclusion that Russian officials near the border in particular are being duped and tricked into opening the files.
Additional malicious files are downloaded
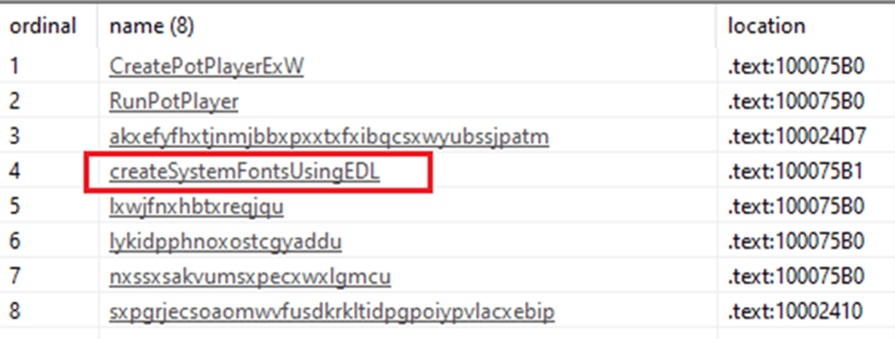
If the malware disguised as a PDF is opened, the application downloads eight malicious files and hides them on the affected computer.
Once done, the program starts infecting the computer and searching for sensitive information. In addition, the software is able to upload files to the Internet and allow attackers to gain access to the system.
For what or for whom “Mustang Panda” collects the data is not officially known and can only be guessed at for the most part. However, since hacker campaigns have already been linked to the Chinese government in the past, the experts also assume a potential connection here.